AWS
<- Return to all blogs
-

STAPI Sprint #4: Interoperability for Satellite Data Ordering
During our most recent STAPI sprint we brought together attendees from across the geospatial industry to discuss interoperability for satellite data ordering.
-
STAPI Sprint #4: Interoperability for Satellite Data Ordering
During our most recent STAPI sprint we brought together attendees from across the geospatial industry to discuss interoperability for satellite data ordering.

-
Introducing Earth Search Console: An AWS Open Data Exploration UI
In this blog, we’ll detail how Earth Search Console leverages FilmDrop, and what Console components we are most excited about.

-
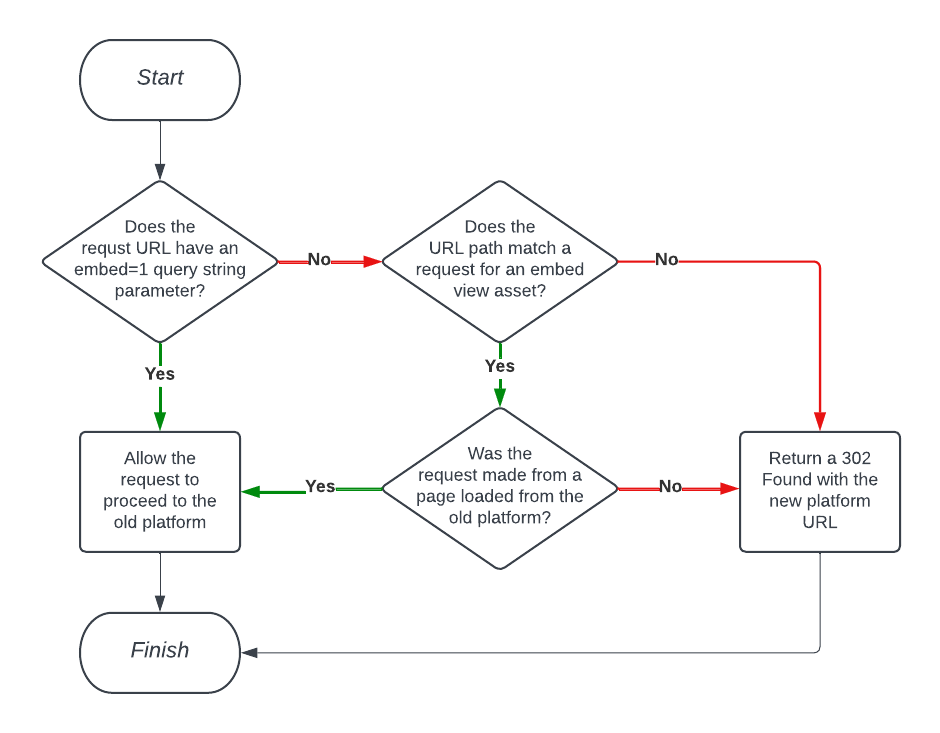
Using Amazon CloudFront Functions to Facilitate Smooth Project Transitions with Conditional Redirects
In this blog, we detail our experience making this project transition possible for our client by implementing conditional redirects via Amazon CloudFront functions.
-
Edge Processing of Drone Data for Search and Rescue using Open Source Tooling on an AWS Snowcone
Element 84 has developed near real-time edge processing of drone and aerial imagery for human identification that leverages machine learning and AWS Snowcone edge capabilities during austere operations for search and rescue applications.

-
AWS re:Invent 2022 Mega Recap
This month our geospatial team traveled to Las Vegas to attend AWS re:Invent and talk about FilmDrop—our cloud-native, geospatial processing suite. Over the course of the week, we had a chance to meet tons of great people and spend time in talks and labs learning as much as we could. We’ve put together a mega…

-
Sentinel-2 Cloud-Optimized GeoTIFFs Now Available on AWS Registry of Open Data
This week, in collaboration with Geoscience Australia, we released our Sentinel-2 Cloud-Optimized GeoTIFF (COG) dataset on AWS Open Data. Our collection contains all 11.4 million scenes from the Sentinel-2 Public Dataset, except the JPEG2000 (JP2K) files are all converted to COGs. Our dataset is continuously updated to mirror the growth of the public Sentinel-2 data…
-
AWS Public Safety and Disaster Response Competency
Hanging just above the reception desk at our office in Alexandria are three framed posters–one for each of our company values. Now you may think that’s a bit cheesy–in a sort of team-rowing-motivational poster kind of way–but they truly drive our work, decision making and business outlook at Element 84. For me, our most important…
-
IAM What IAM And That’s All That IAM
Testing Your IAM Policies As the complexity of your AWS environment grows, the need for more specific Identity and Access Management (IAM) roles, and policies increases. These IAM policies govern not only the users that are logging in to the AWS environment, but also the permissions that are granted to services, Lambda functions, EC2 instances, and…
-
Serverless Devise with Jets
Over the past few years, serverless design has taken the cloud community by storm. It is hard to ignore–with promises like “pay only for what you use”, “no security patching”, and “infinite scalability”. Being on the cutting edge can have drawbacks too, which in this case is what I would describe as an absence of…
-
Rising From The Ashes, Untangling the Mysteries of DevOps
There are many books that have influenced me as a software engineer. From the computer science textbooks I used in college, to the animal covered books from O’Reilly I used to pick up new languages and tools, to the Clean Code books from Uncle Bob Martin that helped shape the way I approach software development. However,…